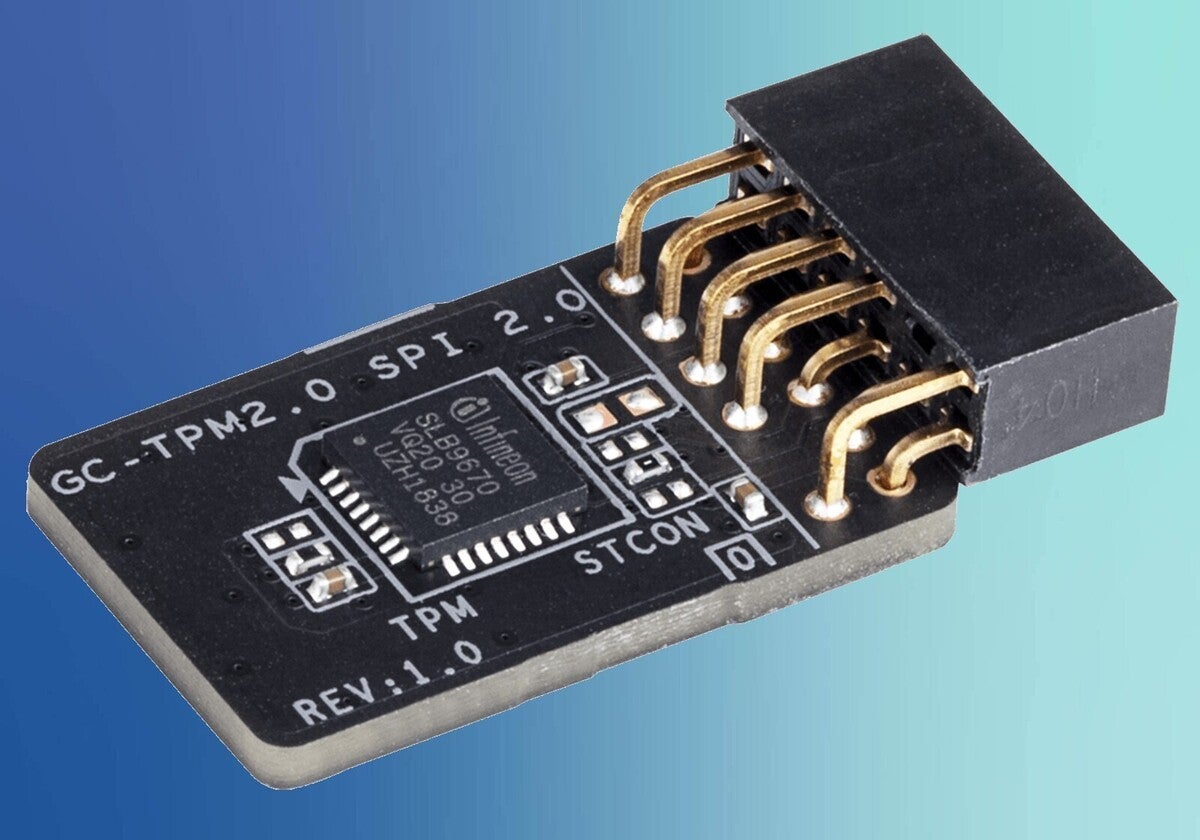
OPTIGA™ TPM (Trusted Platform Module) offers a broad portfolio of standardized security controllers to protect the integrity and authenticity of embedded devices and systems. With a secured key store and support for a variety of encryption algorithms, OPTIGA™ TPM security chips provide robust protection for critical data and processes through their rich functionality.
- Infineon Tpm Slb 9665 Tpm2.0
- Infineon Tpm Professional Package Removal
- Infineon Tpm Professional Package Uninstall Windows 10
- Infineon Tpm Professional Package
The TPM, a secure cryptographic integrated circuit (IC), provides a hardware-based approach to manage user authentication, network access, data protection and more that takes security to higher level than software-based security. This paper explains how to use and enable the TPM in 4 easy steps.
OPTIGA™ TPM security controllers are ideal for platforms running both Windows and Linux andd its derivatives (SLB 9645 product versions for Chrome OS available). Based on Trusted Computing Group (TCG) standards, they support the TPM 1.2 or the latest innovative TPM 2.0 standard.
- A vulnerability in Infineon TPM hardware has been discovered recently with outdated TPM firmware using an algorithm that generates weaker RSA keys. This page provides information on how to update outdated TPM firmware. For more detailed information please refer to the Infineon web site. Empty Microsoft has published additional information.
- Upgrading the Firmware on Infineon TPM's. In early October of 2017, researchers announced, publicly, a cryptographic vulnerability in the RSA generation algorithms found within practically every TPM, using Infineon's RSA library. This vulnerability would effectively allow an attacker to easily guess the private key component of the RSA key.
- Infineon Trusted Platform Module (TPM) Vulnerability (CVE-2017-15361): Impact Status on Dell Products A new Infineon Trusted Platform Module (TPM) vulnerability (CVE-2017-15361) has risen, use this article to find out how to protect your Dell hardware.
In early October of 2017, researchers announced, publicly, a cryptographic vulnerability in the RSA generation algorithms found within practically every TPM, using Infineon's RSA library. This vulnerability would effectively allow an attacker to easily guess the private key component of the RSA key stored within the TPM - rendering the protections and insurances granted by the TPM useless. Turns out, many TPM's actually use Infineon's technologies, meaning many TPM's are vulnerability - including all Asus and Gigabyte TPM's (that I know of).
tl;dr - TPM broke, I sad, TPM need fix.
Since the point of TPM's is to perform key protection inside hardware, a software fix is impossible. This is so difficult to mitigate that Window's just resorts to emitting a warning in the Event Logs like the one below:
Now, 6 months later and over a year since Infineon was notified of this issue, Asus and Gigabyte have yet to release updates for their TPM's. Although, I'm not particularly surprised considering most consumers would likely brick their machine's when trying to update (or not need to update to begin with). Thankfully, many enterprise-centered company's use these Infineon based TPM's, meaning we, the consumers, can piggyback off of enterprise clients shouting for a fix.
In this case, it turns out that the Asus and Gigabyte TPM's are effectively the same one's found in some Supermicro servers, and of course, Supermicro had to release firmware updates - updates that we can use.
Getting Started
Before I get started, I want to make sure the TPM is working in my device. I can ask Window's about it via the Get-TPM command.
Getting the Firmware
Everything looks good! Now to get the firmware. I found a compatible version on Supermicro's driver site (Driver FTP).
Looking through the files extracted files, there are two directories:
The important files are these:
I'm going to copy the above to the same folder, because I'm lazy.
Now .workspace contains the following files:
Infineon Tpm Slb 9665 Tpm2.0
Now to upgrading the firmware!
Upgrading the Firmware
Let's make sure TPMFactoryUpd.exe detects the TPM.
And it does, sweet! Now to run the upgrade.
Sad panda, it turns out we need to disable the TPM module in the BIOS/UEFI before we can flash the firmware update. Time to connect my Spider KVM and boot into the UEFI menu. BTW, Spiders are awesome, but don't pay full price!
Now to disable the TPM.
After booting back into Windows, it looks like disabling the TPM fixes the Empty Buffer problem:

Now I can try to update the TPM again.
Infineon Tpm Professional Package Removal
And it works!
Wrapping Things Up
A disabled TPM is rather useless, time to boot back into the UEFI menus to enable it.
And since this vulnerability is for RSA key generation, it's best to reset all generated keys. I used a TPM clear to do this, plus a reboot.
After getting back into Windows, I'm greeted with a lovely success message.
And as a final check, it looks like the ManufacturerVersion was updated to 5.62.
Infineon Tpm Professional Package Uninstall Windows 10
Infineon Tpm Professional Package
Yeah, no more weak keys!